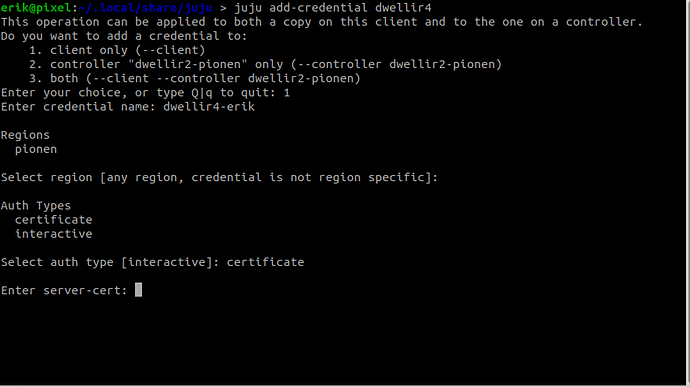
The current process I use for a client when adding a new LXD host (cloud) to an existing controller is as follows and will automatically add certificates to the client “credentials.yaml”:
Adding a lxd cloud to an existing controller
Temporarily have admin enable password authentication on the remote lxd if you have disabled it as part of a production grade installation (this is not needed if lxd-admin already has added the client.crt) in the lxc remote (lxc config trust add client.crt), but this is the easy-but-not-as-secure-version:
lxc config set core.trust_password 12345678
On the client, add the new LXD host as a remote:
lxc remote add new-cloud 192.168.1.44
Make sure you are “admin” on the controller (my-controller).
juju switch my-controller
juju whoami
Controller: my-controller
Model: controller
User: admin
Now, lets add this new (lxd) cloud to the (juju) controller which the client is already aware of since we added it as a lxd remote.
juju add-cloud new-cloud my-controller
On the juju client (make sure you have run lxc locally first, such that your ~/snap/lxd/common/config/client.crt file is available. This is needed by juju autoload-credentials which will take care of adding the credentials to the client and controller.
juju autoload-credentials
Select 3 if this is a new client as we want to add both locally and in the controller. Select the proper credential and give it a name, lets say “cred00”
Test that admin can create a new model (the first model must also be told explicitly to use your new credential:
juju add-model my-model new-cloud --credential cred00
When this works, users needs now also be granted possibility to use the cloud or it wont show up in the “juju clouds” and no models can be deployed to it by users that are not granted add-model access.
juju grant-cloud erik-lonroth add-model my-cloud
If you logout and repeat the process for a second user, the new cloud should be available to it aswell.
juju logout
juju login -u erik
juju clouds
$ juju clouds
Only clouds with registered credentials are shown.
There are more clouds, use --all to see them.
Clouds available on the controller:
Cloud Regions Default Type
iceberg 1 default lxd
new-cloud 1 default lxd
Clouds available on the client:
Cloud Regions Default Type Credentials Source Description
aws 19 us-east-1 ec2 2 public Amazon Web Services
dwellir 1 default lxd 1 built-in LXD Cluster
google 20 us-east1 gce 1 public Google Cloud Platform
iceberg 1 default lxd 1 local LXD Container Hypervisor
localhost 1 localhost lxd 1 built-in LXD Container Hypervisor
new-cloud 1 default lxd 1 built-in LXD Cluster
Have admin lock down the lxd-host again so it will not be open with an easy password!
lxc config unset core.trust_password
I’m not sure this process can be simplified, but I think this is the best I’ve been able to produce so far.